Americans value privacy. We close and lock our doors when we get home at the end of the day. We close the blinds when we change clothes so the neighbors can’t peek. If someone wants to visit, they don’t just come over unannounced–they call or text first. In terms of technology, we set passcode locks on our computers and smartphones.
A 2014 Pew Research poll asked people to define “privacy” in one word. The most popular answers were security, secret, personal, alone, information and business.
But today, it’s possible to follow your Internet searches, see who you email, text and call, track your geographical location at all times, monitor your purchases and even track your credit card and phone bills.
The trackers include everyone from family and friends to companies, marketing agencies, the government and law enforcement. From basic information posted on social media, to GPS tracking on your smartphone, people around the world can learn a lot about you from your Internet activity — even when you aren’t intentionally on the Internet. Combining these various components gives them a pretty good idea of what you do, your likes and dislikes, and who and where you are.
You know that nightmare where you’re standing naked in front of an audience? Well, this is the very real 21st century equivalent.
Nearly every app on the modern smartphone is programmed with GPS. Whenever you walk by a WiFi-enabled store, café or home with your Wi-Fi turned on, it registers your device– creating a virtual path of your movement. Do you ever search Google for something, and minutes later see advertisements for it on your sidebar or Facebook? That’s not a coincidence.
In 1965 Gordon Moore, co-founder of Intel, made a prediction known as Moore’s Law: computing power doubles every two years. In other words, computers process large amounts of data faster than ever before. That’s why those Google searches turn into ads so quickly.
Further, the price of data storage is steadily dropping. In 1991, one-gigabyte hard drives cost around $2,700. In 2007, one terabyte (1000x GB) hard drives cost $375. Currently, one terabyte drives cost around $60.
What happens when infinitely faster processing meets infinitely cheaper storage?
“It starts to infringe upon privacy,” said Paul Rosenzweig, cyber and homeland security expert.
So what right do Americans have to privacy?
The Founding Fathers wrote the Fourth Amendment to the Constitution in 1791. It grants citizens the right to be “secure in their persons, houses, papers, and effects, against unreasonable searches and seizures.” Obviously they didn’t have Internet security in mind. Instead, it was a response to Britain’s “general warrant” allowing soldiers total access to search American colonials and their homes.
Let’s translate this to cybersecurity: without a warrant, the government cannot keep surveillance on devices for which individuals have a reasonable expectation of privacy. It also cannot physically take these devices to later use as evidence in court.
Fast-forward nearly 200 years to the Privacy Act of 1974. This legislation came after concerns about the government’s collection, retention and use of personal data. The federal government has a number of databases with information on individuals, both citizens and noncitizens.
The Privacy Act of 1974 set four basic restrictions on the government regarding these databases. First, it required government agencies to show individuals all records kept on them if requested. Second, it set “fair information practices” that agencies must follow when collecting and saving data, such as giving notice that it is collecting the information, how it is storing it and how it is protecting privacy. Third, it restricted the ways information can be shared with other people and agencies. Fourth, it allowed people to sue the government if it violates these regulations.
Even though the Privacy Act was meant to increase government transparency, it contains many exceptions and loopholes.
For example, nongovernment entities, like email and phone providers and app developers are barely restricted when it comes to information collection. They are legally required to disclose in privacy agreements the information they collect (yes, those long, size five-font agreements that very few people bother to read), but that’s about as far as regulation goes. Further, these companies are required to provide government agencies with these user records whenever requested, leaving virtually no choice.
That’s why privacy advocates like Amie Stepanovich encourage companies to only collect information completely pertinent to the functioning of the business.
Stepanovich is senior policy counsel at Access Now, an international digital rights organization.
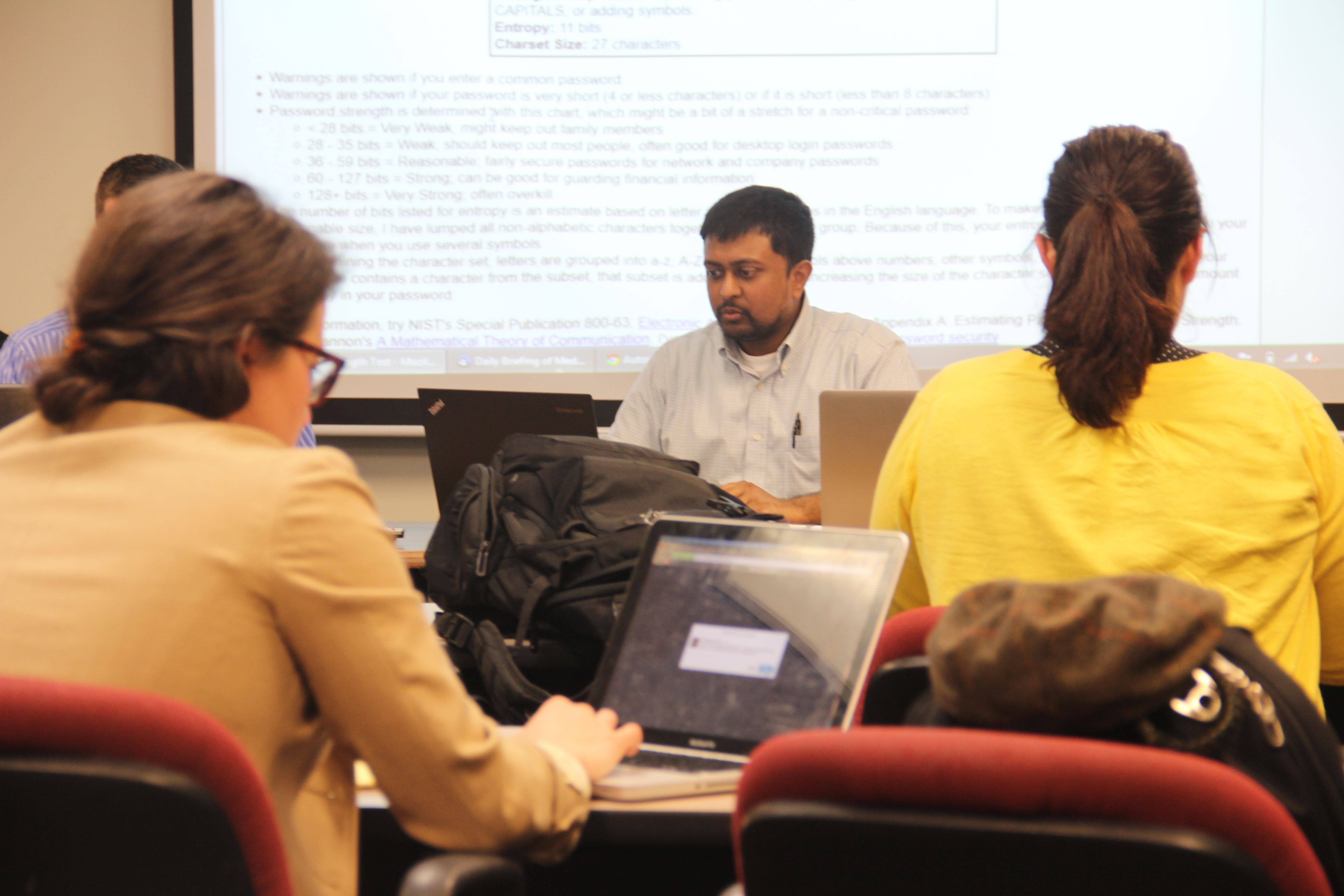
Stepanovich also urges further safeguards for personal privacy, such as encrypting emails, turning off smartphone app location services and creating secure passwords for online accounts. While these precautions–ranging from simple to very skillful–can certainly aid in Internet security, there’s no surefire way to be anonymous online.
Privacy professionals know that it’s impossible to function in 21st century society without being active online. They also know that, though it means being tracked, keeping location services turned on for some apps can make life easier and, honestly, more fun. Who wants to carry around–and decipher– a map when a GPS provides voice activated turn-by-turn directions? Similarly, think about apps like Starbucks’ that send alerts and coupons every time you’re near a store.
We’re okay with giving Starbucks our location, and maybe even letting Google track our searches, if it means we’ll be notified of sales. But when did we consent to give our purchase histories to credit companies, address histories to data aggregation companies, or travel habits and telephone records to the government?
Americans have mixed feelings about digital surveillance. Many are willing to sacrifice some privacy in exchange for stronger national security. Wouldn’t we all rather the government use cyber tracking to identify and stop terrorists through before they attack?
But specifically after the Snowden leaks, many Americans have become skeptical of the government’s digital surveillance. The Pew Research poll found that 80 percent of adults believe Americans should be concerned about the government monitoring their phone and Internet activity.
Even more are concerned with company surveillance. That same poll showed that 91 percent of adults “agree” or “strongly agree” that consumers have lost control over how companies collect and use their personal information.
While 61 percent said they would “like to do more” to protect their anonymity online, 76 percent consider that a difficult feat.
Others don’t find any reason for online anonymity.
The “I have nothing to hide” argument is a popular one. But critics say no one wants their entire life exposed, no matter how “good” of a person they are.
Too much privacy may enable corrupt behavior. Too little privacy may bring Orwell’s Big Brother to reality. People act differently when they know they’re being watched, and Americans are being watched now more than ever before.
In 1999, SUN Microsystems CEO and founder Scott McNealy famously said, “You have zero privacy anyway. Get over it.” We may be moving that way.